Table of Contents
Artificial Intelligence is evolving fast. But we are now entering a new phase Agentic AI Pindrop Anonybit.
Unlike traditional AI systems that wait for commands, Agentic AI systems act independently, make decisions in real time, and execute tasks autonomously.
In cybersecurity and digital identity, this shift is revolutionary.
Two companies leading this transformation are:
- Pindrop
- Anonybit
This blog explores how Agentic AI works, why it matters in 2026, and how Pindrop and Anonybit are building autonomous security infrastructures.
What is Agentic AI : Pindrop Anonybit?
Agentic AI refers to AI systems designed to function as autonomous agents.
Instead of simple automation, Agentic AI systems:
- Understand context
- Set goals
- Make decisions
- Take actions
- Continuously learn from outcomes
In cybersecurity, this means AI doesn’t just detect threats it responds instantly without waiting for human approval.
This is critical in today’s world of AI-generated fraud and deepfake attacks.
Why Agentic AI is Critical in Cybersecurity
Cybercriminals now use:
- AI voice cloning
- Deepfake video scams
- Synthetic identities
- Automated fraud bots
Traditional security systems are reactive and rule-based.
Agentic AI is:
- Proactive
- Self-improving
- Adaptive
- Autonomous
When milliseconds matter, human-led systems are too slow.
Agentic AI fills that gap.
Pindrop: Agentic AI for Voice Security
About Pindrop
Pindrop specializes in voice authentication and fraud detection for enterprises, especially financial institutions and call centers.
Official website:
https://www.pindrop.com
Pindrop focuses on:
- Voice biometrics
- Fraud detection
- Deepfake voice identification
- Contact center security
How Pindrop Uses Agentic AI
Pindrop’s AI systems function like autonomous fraud investigators.
Here’s how:
1. Real-Time Voice Analysis
Every call is analyzed in milliseconds. The system examines:
- Acoustic fingerprints
- Background noise
- Frequency irregularities
- Voice consistency
2. Deepfake Detection
With the rise of generative AI tools, voice cloning is becoming common. Pindrop’s models detect synthetic artifacts invisible to human ears.
3. Autonomous Risk Scoring
Instead of alerting humans first, the AI:
- Assigns fraud risk scores
- Triggers step-up authentication
- Blocks suspicious transactions
This is Agentic AI in action : autonomous decision-making.
Real-World Example
Imagine a bank call center.
A fraudster uses AI-generated voice cloning to mimic a customer.
Pindrop’s Agentic AI:
- Detects subtle inconsistencies
- Flags synthetic speech
- Automatically prevents account access
No manual review required.
Damage prevented instantly.
Anonybit: Agentic AI for Decentralized Biometric Identity
About Anonybit
Anonybit is pioneering decentralized biometric authentication.
Official website:
https://www.anonybit.io
Anonybit focuses on:
- Passwordless authentication
- Decentralized biometrics
- Privacy-first architecture
- Zero-knowledge identity systems
The Problem with Traditional Biometrics
Most systems store biometric data in centralized databases.
If breached:
- Fingerprints are compromised forever
- Facial data cannot be reset
- Voice prints become liabilities
Centralized biometric storage is a high-value target for hackers.
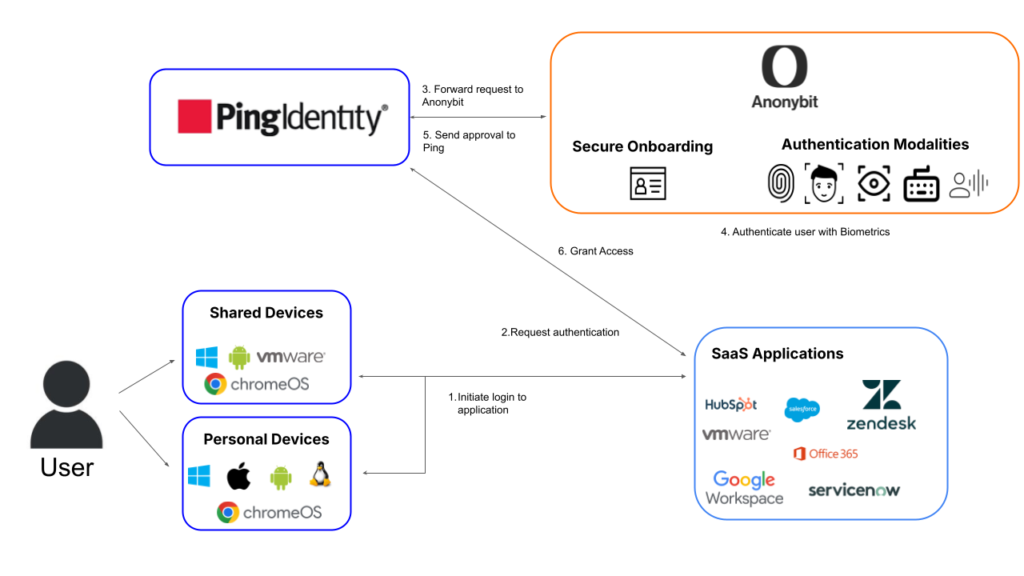
How Anonybit Uses Agentic AI
Anonybit combines decentralized infrastructure with intelligent AI agents.
1. Biometric Fragmentation
Instead of storing full biometric templates:
- Data is split into encrypted fragments
- Distributed across nodes
- Reconstructed only during authentication
2. Continuous Authentication
Agentic AI monitors user behavior dynamically:
- Device patterns
- Interaction style
- Biometric consistency
If anomalies appear, the system autonomously increases verification requirements.
3. No Single Point of Failure
Because data is decentralized:
- A breach in one node reveals nothing
- Identity theft risk drops significantly
This is next-generation AI-driven identity security.
Agentic AI vs Traditional AI in Security
| Feature | Traditional AI | Agentic AI |
|---|---|---|
| Decision Making | Rule-based | Autonomous |
| Speed | Delayed | Instant |
| Adaptability | Limited | Continuous learning |
| Fraud Response | Manual escalation | Automatic action |
| Risk Prevention | Reactive | Proactive |
Agentic AI doesn’t just detect problems — it resolves them in real time.
Why This Matters in 2026
We are entering an era where:
- Deepfake scams are scalable
- Voice cloning tools are publicly accessible
- Identity fraud is AI-powered
Organizations need AI defenders that:
- Think independently
- Act instantly
- Adapt continuously
Companies like Pindrop and Anonybit are building that future.
The Future of Agentic AI in Identity & Security
Over the next few years, expect:
- Multi-modal biometric authentication (voice + face + behavior)
- AI agents negotiating risk thresholds dynamically
- Fully autonomous zero-trust frameworks
- Self-healing cybersecurity systems
Agentic AI will become foundational to digital infrastructure.
Frequently Asked Questions (FAQ)
What is Agentic AI?
Agentic AI refers to AI systems that can independently make decisions and take actions without constant human guidance.
How does Pindrop detect deepfake voices?
Pindrop analyzes acoustic anomalies and synthetic artifacts in voice signals using advanced AI models.
What makes Anonybit different?
Anonybit decentralizes biometric data, eliminating centralized storage risks and improving privacy protection.
Is Agentic AI better than traditional AI?
Yes. Agentic AI provides autonomous, proactive, and adaptive defense mechanisms.
Can Agentic AI prevent identity fraud?
It significantly reduces fraud risk by detecting anomalies and responding instantly.
Final Thoughts
Agentic AI represents the next evolution of artificial intelligence.
In cybersecurity and digital identity, autonomy is not a luxury. it is a necessity.
With:
- Pindrop securing voice ecosystems
- Anonybit decentralizing biometric authentication
We are moving toward a future where AI doesn’t just assist it protects.
As fraudsters use AI to attack, enterprises must use Agentic AI to defend.
The battle of intelligence has begun and autonomous systems are leading the way.

